In today’s digital age, where the internet plays a pivotal role in our daily lives, the importance of user authentication cannot be overstated. User authentication is the process by which a website verifies the identity of its users, ensuring that only authorized individuals gain access to sensitive information or perform certain actions. In this article, we will explore the best practices for implementing robust user authentication on your website to protect user data and enhance security.
By implementing these user authentication best practices, you can enhance the security of your website, protect user data, and build trust with your audience in an increasingly digital world.
The Significance of User Authentication
User authentication serves as the digital gatekeeper to your website’s inner sanctum. It’s akin to the sentry guarding a fortress, ensuring that only those with legitimate credentials gain access. In a cyber landscape teeming with malicious actors, this gatekeeper role is pivotal in safeguarding sensitive user information, financial transactions, and intellectual property.Security Threats in the Digital Landscape
The digital landscape is not without its lurking threats. Hackers, scammers, and cybercriminals continually devise new tactics to compromise user accounts and exploit security vulnerabilities. From the deceptive artistry of phishing attacks to the brute force tactics of determined hackers, the need for robust user authentication becomes ever more evident.The Fundamentals of User Authentication
What Is User Authentication?
The height of your workstation is quite important for keeping good posture. Make sure your workstation is at the proper height so that your knees make a 90-degree angle and your feet are flat on the floor. Consider utilizing a footrest to obtain the optimum posture if your desk is not adjustable.
Why It Matters for Websites
User authentication is the guardian of your digital realm. It not only keeps intruders at bay but also protects your users’ valuable data and ensures that your website remains a trusted and secure destination.Password Best Practices
Strong Password Creation
Creating a strong password is the first line of defense. Encourage users to craft passwords that are as unique as their fingerprints. They should incorporate a mix of uppercase and lowercase letters, numbers, and special characters, forming an uncrackable code.Password Storage and Encryption
Storing passwords securely is paramount. Hashing algorithms, such as bcrypt or Argon2, should be employed to convert passwords into unreadable gibberish even if the database is breached. Encryption techniques add an extra layer of defense to safeguard these hashed passwords.Password Policies and Complexity Requirements
Implementing password policies that enforce complexity requirements and regular password changes is essential. Policies can thwart attackers who rely on easily guessable passwords and outdated credentials.Multi-Factor Authentication (MFA)
Understanding MFA
Multi-factor authentication, or MFA, represents the future of digital fortification. It necessitates multiple forms of verification, ensuring that even if a hacker cracks the password, they’re still left knocking at the door.Types of MFA
From SMS codes to authenticator apps and biometric scans, explore various MFA methods. The goal is to find the balance between security and user convenience that suits your website’s needs.Implementing MFA on Your Website
Integrating MFA into your website’s authentication process requires careful planning. It should enhance security without making the login process overly cumbersome for users.Biometric Authentication
The Role of Biometrics
Biometrics have stepped into the limelight, offering futuristic authentication methods. Fingerprints, facial recognition, and iris scans are the keys to unlocking secure user experiences.Biometric Authentication Methods
Each biometric modality brings its strengths and weaknesses to the table. Dive into their applications and limitations in the realm of website security.Pros and Cons of Biometric Authentication
Biometrics offer unparalleled security and convenience, but they also introduce privacy concerns and may not be universally accessible on all devices.Single Sign-On (SSO)
Streamlining User Access with SSO
Single Sign-On simplifies the digital journey for users, sparing them the hassle of managing multiple sets of credentials. It’s the golden ticket to accessing a network of services with a single, secure login.Benefits of SSO
Explore the benefits of SSO, including improved user experiences, enhanced security, and centralized control over access management.Considerations When Implementing SSO
While SSO offers numerous advantages, it’s not without challenges. Understand the considerations and potential stumbling blocks when implementing this technology.OAuth and OpenID Connect
Overview of OAuth and OpenID Connect
OAuth and OpenID Connect are two protocols that facilitate secure authentication and authorization processes in the digital world. Delve into their inner workings to grasp their significance.Use Cases and Advantages
Discover the versatility of OAuth and OpenID Connect. They are the keys that unlock secure, interoperable authentication and authorization across platforms.Security Considerations
While these protocols offer great power, they also come with security responsibilities. Learn about best practices and potential risks associated with their implementation.Account Lockout and Brute Force Protection
Preventing Unauthorized Access Attempts
Shield your authentication process against relentless attackers by implementing account lockout mechanisms. Brute force protection keeps adversaries at bay by limiting login attempts.Strategies for Account Lockout and Brute Force Protection
Strike a balance between security and usability. Implement strategies that effectively deter attackers while ensuring genuine users can access their accounts.Security Headers and Protocols
HTTP Security Headers
HTTP security headers, like Content Security Policy (CSP) and HTTP Strict Transport Security (HSTS), serve as guardians against common web vulnerabilities. Explore their roles in fortifying your website’s security.HTTPS and TLS
Encrypting data in transit is non-negotiable. HTTPS, coupled with Transport Layer Security (TLS), guarantees secure communication between users and your website, thwarting eavesdropping and man-in-the-middle attacks.Content Security Policy (CSP)
CSP is your shield against cross-site scripting (XSS) attacks and other client-side vulnerabilities. Understand how it works and how to configure it to protect your website.User Education and Awareness
Training Users for Secure Practices
An informed user is your greatest ally in the battle for security. Educate your users about recognizing phishing attempts, creating strong passwords, and staying vigilant online.Communicating Security Measures
Transparency breeds trust. Communicate your website’s robust security measures to reassure users and inspire confidence in your platform.Monitoring and Auditing
Continuous Security Monitoring
Security is an ongoing process. Implement tools and practices for continuous monitoring to detect and respond to security threats in real-time.Conducting Security Audits
Regular security audits are your proactive defense. Periodically assess your website’s authentication mechanisms, identify vulnerabilities, and ensure compliance with best practices.Conclusion
Recap of Best Practices
The foundation of user authentication best practices is an essential pillar of a secure online ecosystem. Recap the key takeaways from this article, reinforcing the importance of these measures in safeguarding your website and user data.Continuous Improvement in User Authentication
Highlight the dynamic nature of cybersecurity and the need for ongoing adaptation and improvement in user authentication practices. Emphasize that security is a journey, not a destination, and staying ahead of evolving threats is paramount to a safe online experience.
By embracing these user authentication best practices, you fortify your website’s defenses, protect your users, and contribute to a more secure digital landscape for all.
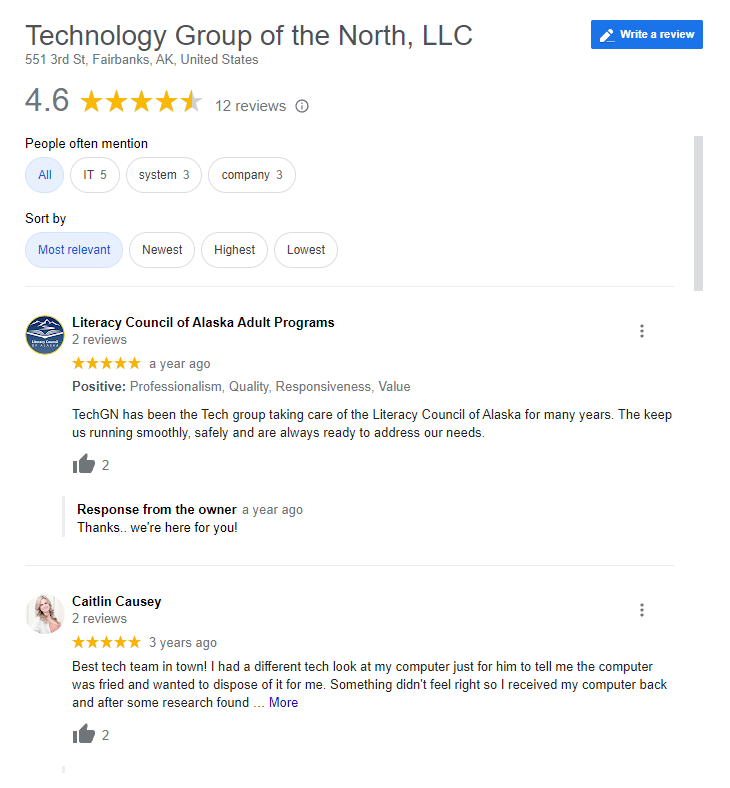
Reviews