Attacks such as Distributed Denial of Service (DDoS) have grown more dangerous in the connected digital age. In these attacks, criminal actors plan a concerted attack to overwhelm a target system or network with traffic, blocking it from being accessed by authorized users. All sizes of people, businesses, and organizations must comprehend the risks posed by DDoS attacks. This article seeks to clarify the subtleties of DDoS attacks by describing the different shapes they can take and the significant effects they may have on their targets.
Types of DDoS Attacks
There are three main types of DDoS attacks, each with distinct traits and means of inflicting havoc.Volumetric Attacks
By saturating a target’s network bandwidth with an excessive amount of traffic, these attacks seek to do so. The network infrastructure is overwhelmed by the volume of this traffic, making it unable to handle valid user requests. Imagine a network buckling under the weight of a data tsunami that is crashing over its shores.Application Layer Attacks
These attacks go after a network stack’s application layer. They concentrate on utilizing weaknesses in web programs, including login pages or search functionalities, to use up a lot of server resources. Similar to an endless stream of seemingly benign requests, this kind of assault wears down the system over time.Protocol Attacks
Protocol attacks focus on the network infrastructure itself, looking to take advantage of flaws in the protocols or hardware used for networking. Attackers can wreak havoc by interfering with the network’s routine operations by focusing on certain vulnerabilities. Protocol attacks resemble breaking into a large network’s control panel and messing with the gears and levers to wreak havoc.DDoS Attack Mechanisms
The effectiveness of a DDoS attack depends on a number of crucial techniques used by hackers to increase their impact.Botnets
Botnets, large networks of infected computers, cellphones, or Internet of Things (IoT) devices, are at the center of many DDoS attacks. These captured machines, often known as “bots” or “zombies,” can be managed remotely by the assailant. When directed, they launch a planned assault on the target, escalating the attack’s size. Consider botnets as a puppeteer manipulating many marionettes to accomplish a nefarious purpose.Amplification
Network protocol manipulation is used in amplification techniques to establish a feedback loop. A susceptible server receives a modest request from an attacker, which it then reacts to by sending a considerably bigger reply to the victim’s IP address. The amount of traffic aimed towards the target is amplified and becomes overwhelming as a result. A megaphone used to turn a whisper into an audible roar is analogous to amplification.Spoofing
Attackers frequently use IP spoofing to avoid detection and attribution. Using this method, the attacking packets’ source IP addresses are forged to make it look as though they came from reliable sources. Attackers might make it harder for defenders to identify the attack’s origin by concealing their identities in this way. Since spoofing is a master of disguise, it can be difficult to spot the real aggressor in a crowded space.Targets of DDoS Attacks
DDoS attacks are equal-opportunity enemies that target a variety of targets:
- E-commerce Websites: producing a disruption in online sales and financial losses.
- Financial Institutions: disrupting the operations of internet banks.
- Gaming Companies: frustrating players and having an impact on multiplayer games.
- Government Websites: causing public services to be disrupted and eroding trust.
- Critical Infrastructure: Targeting transportation or electricity grids can have disastrous repercussions.
The Dangers Posed by DDoS Attacks
Being the target of a DDoS attack has serious, varied repercussions.Disruption of Services
The interruption of services poses the most immediate and evident threat. Legitimate users are unable to access the services or resources they require when a target is overrun by a DDoS attack. This protracted downtime can cause enormous financial losses and reputational harm to a business.Financial Losses
Financial losses result immediately from downtime. When an organization’s internet operations are suspended, revenue is lost. In addition, they might spend more money on incident response, recovery work, and potential legal liability.Reputational Damage
A valuable resource in the digital age is trust. A DDoS attack can undermine client confidence and damage a brand’s reputation. Customers who experience service interruptions or security issues are likely to look for alternatives, which could lead to a long-term loss of revenue.Legal and Regulatory Consequences
Strict regulatory obligations for data protection and cybersecurity apply to many businesses. Legal repercussions, penalties, and sanctions may result from inadequate defense against DDoS attacks. Additionally, customers who experience service interruptions may file lawsuits against businesses.Recognizing the Signs of a DDoS Attack
Early DDoS attack detection is essential for effective response and mitigation.Unusual Traffic Patterns
A DDoS attack is frequently identified by an unexpected and large surge in network traffic. This data frequently displays patterns that are different from typical user activity, including an increase in requests coming from a particular region.Website and Network Performance Degradation
The performance of a website and the network may rapidly deteriorate as a DDoS attack progresses. When trying to access online resources, users may run into issues such as poor loading times, unresponsiveness, or timeouts.Unexplained Outages
A DDoS assault may be underway if websites or services are suddenly inaccessible for no apparent reason. Any downtime that cannot be ascribed to regular maintenance or technical problems needs to be looked into right away.Increased Network and Server Resource Utilization
Monitoring server and network resource usage can spot indications of stress brought on by a DDoS assault. Increases in CPU, memory, or bandwidth utilization that are unusual can be a sign of a persistent attack.Mitigation Strategies
Organizations must combine proactive measures with response techniques to effectively fight against DDoS attacks.Network Security Measures
Intrusion Detection Systems (IDS)
These systems analyze network traffic in real-time, looking for patterns that correspond to known attack fingerprints or abnormalities. An IDS can provide notifications when suspicious activity is found to allow for more investigation.Intrusion Prevention Systems (IPS)
By actively blocking malicious communications or attackers based on specified criteria, IPS builds upon IDS and takes it a step further. The impact of attacks can be greatly diminished by this real-time defense.Traffic Filtering
Organizations can filter out harmful traffic before it enters their networks by using traffic filtering technologies and firewalls. This is especially helpful for reducing the impact of volumetric attacks and for preventing traffic from recognized botnets.Content Delivery Networks (CDNs)
Traffic is divided among a network of servers that are spread out geographically to operate content delivery networks. By doing this, CDNs can block the origin server from receiving a sizable percentage of DDoS traffic. This tactic enhances the overall functionality and load times of the website while also assisting in maintaining service availability during an attack.Load Balancing
Solutions for load balancing evenly distribute incoming traffic among several servers. They do this to avoid having any one server become overloaded during a DDoS assault. Through the use of load balancers, abnormal traffic patterns can be identified and traffic diverted away from the offending server to maintain service.Cloud-Based DDoS Protection Services
Organizations looking for strong security are increasingly choosing cloud-based DDoS protection services. Before DDoS traffic reaches the target network, these services filter and absorb it using the scale and knowledge of cloud providers. Organizations are able to sustain service availability even amid the most intense DDoS attacks thanks to the dumping of traffic to the cloud.Incident Response Plan
Both preparing for and responding to a DDoS assault are crucial. The amount of outage and recovery time can be greatly decreased by creating an incident response plan that includes roles, duties, and procedures for dealing with a DDoS attack. A good plan should outline how to detect an attack, put mitigation measures in place, and communicate with key stakeholders.Proactive Steps to Prevent DDoS Attacks
Organizations must implement efficient mitigation solutions, but they must also take proactive measures to lessen their susceptibility to DDoS attacks.Regular Vulnerability Assessments
To find and fix vulnerabilities in network infrastructure, online applications, and services, conduct routine security assessments. Quickly apply patches to any known vulnerabilities.Security Patch Management
Applying security patches and upgrades to software, operating systems, and network hardware requires constant attention. Systems that haven’t been patched are more vulnerable to abuse.Employee Training
Employees who receive cybersecurity awareness training might assist avoid unintentional involvement in DDoS assaults, such as falling for phishing scams or unknowingly joining a botnet.Rate Limiting and Traffic Shaping
To effectively control incoming traffic, employ rate limitation and traffic shaping strategies. By making it more difficult for attackers to overburden network resources, these steps can aid in preventing attacks.Post-Attack Analysis and Reporting
Organizations must take a methodical strategy following a DDoS assault to deal with the fallout:Gathering Forensic Data
It’s critical to compile as much forensic information as you can after an assault. This contains server logs, traffic logs, and any other pertinent data. This data can be analyzed to determine the origin and tactics of the attack.Reporting to Authorities
Organizations may need to notify an attack to the appropriate authorities and law enforcement agencies, depending on its size and nature. Working with the police can make it easier to find and bring the attackers to justice.Implementing Post-Incident Changes
After the attack has been contained, it is crucial to assess the organization’s security posture and make the required adjustments to guard against future intrusions. This could entail strengthening incident response processes, network architecture, or security policy.Case Studies
Let’s look at a few real-world case studies to better understand DDoS assaults and their mitigation:Case Study 1: The Mirai Botnet
A well-known example of this is the Mirai botnet, which used IoT devices to build a sizable botnet army. It carried out horrifying strikes in 2016 that interrupted important internet services, demonstrating the scope and potential harm of DDoS attacks. The event made it clear how crucial it is to secure IoT devices and put effective DDoS mitigation methods in place.Case Study 2: Cloud-Based DDoS Protection
A sophisticated DDoS attack on a financial institution put its online banking services in jeopardy. The institution was able to deflect and absorb the assault flow by using a cloud-based DDoS protection technology, providing users with unhindered access.Bottom Line
DDoS assaults are extremely dangerous and should not be taken lightly. These malevolent efforts have the potential to impair services, cause large financial losses, harm reputations, and have legal ramifications. However, organizations may greatly improve their resilience to this constantly changing danger by comprehending the nuances of DDoS attacks and putting in place a thorough approach that combines proactive prevention, efficient mitigation, and post-attack analysis.
The pillars of protection against the never-ending wave of DDoS attacks in the digital sphere are knowledge, planning, and a dedication to cybersecurity.
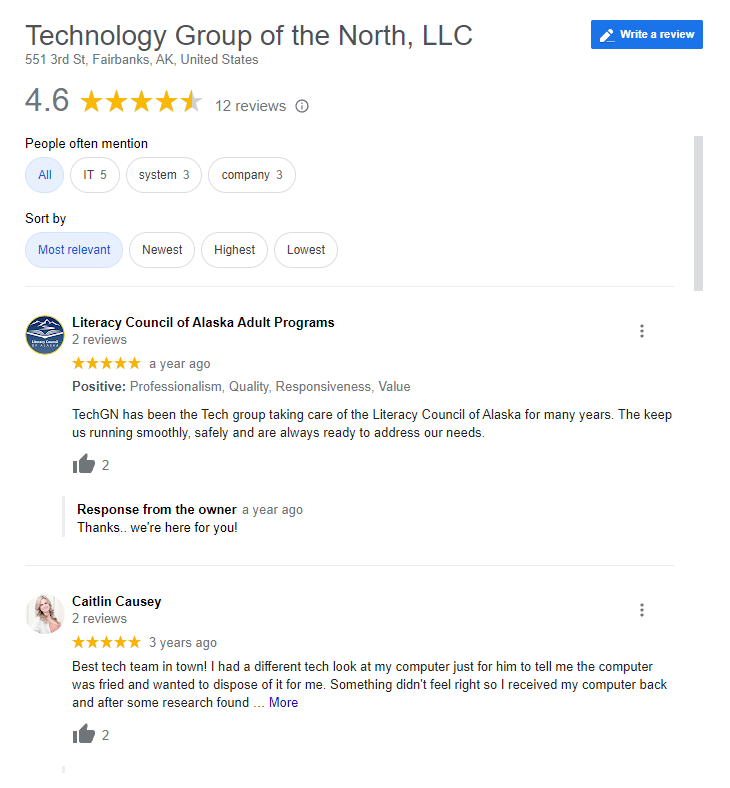
Reviews