Networking, usually referred to as computer networking, is the process of moving data between nodes in an information system through a common media. Networking includes managing, maintaining, and running the network infrastructure, software, and rules in addition to designing, building, and using the network.
Computer networking allows for the connection of endpoints and devices to one another on LANs as well as to larger networks like the internet or private wide area networks (WAN). For service providers, enterprises, and customers all across the world, this function is crucial for resource sharing, using or providing services, and communicating. Everything is made possible via networking, including phone conversations, text messages, streaming videos, and the Internet of Things (IoT).
The complexity of a particular network directly relates to the level of expertise needed to operate it. A major organization, for instance, can have thousands of nodes and strict security specifications, such as end-to-end encryption, necessitating the use of expert network administrators to manage the network.
On the other hand, with a brief instruction booklet, a layperson may set up and carry out basic troubleshooting for a home Wi-Fi network. These instances are examples of computer networking.
Types of networking
Wired networking and wireless networking are the two main categories of computer networking.
Wired networking demands that data be sent between nodes using a physical media. Because to its low cost and dependability, copper-based Ethernet cable is frequently utilized in households and companies for digital communications. As an alternative, optical fiber is utilized to move data farther and quicker, but it comes with a number of drawbacks, such as higher costs and more delicate parts.
Wireless networking enables devices to be connected to a network without any wiring by using radio waves to carry data over the air. The most popular and commonly used type of wireless networking is wireless local area networks (LANs). Microwave, satellite, cellphone, and Bluetooth are a few alternatives.
In general, wired networking is faster, more dependable, and more secure than wireless networks, which typically offer better adaptability, mobility, and scalability.
It should be emphasized that these networking methods focus on the network’s physical layer. Moreover, networking can be divided into categories based on the architecture and design used, including overlay networks and software-defined networking (SDN). LAN, campus, WAN, data center, and storage area networks are just a few examples of the different environments and scales that networking can take.
Components of Computer Network
Network Devices
Computing devices that need to be connected to a network are known as network devices or nodes. Some network gadgets are:
Switches: Repeaters are electrical devices that receive network signals and clean or enhance them, much like transformers are to electricity grids. Repeaters with several ports are called hubs. They distribute the data to any open ports there may be. Bridges are more intelligent hubs that only transmit data to the intended port. A switch is a bridge with many ports. To enable connectivity with numerous network devices, switches can accept multiple data cables.
Mobile phones, laptops, and other consumer electronics: Users often and directly visit these endpoints. For instance, an email is created using the mail program on a laptop or smartphone.
Gateways: Hardware components known as gateways serve as ‘gateways’ between two different networks. These could be servers, routers, or firewalls.
Servers: The primary computing and data storage take place on these application or storage servers. The servers receive all requests for particular operations or data.
Routers: The process of routing involves choosing the network path that data packets will take. These packets are sent by routers between networks in order to get to their destination. They boost the effectiveness of big networks.
Network Defense
Communication protocols
All nodes involved in the information transfer must abide by a set of rules known as a communication protocol. The internet protocol suite (TCP/IP), IEEE 802, Ethernet, wireless LAN, and cellular standards are a few examples of popular protocols. A theoretical paradigm called TCP/IP standardizes communication in a contemporary network. It proposes that these communication linkages have four functional layers:
- Transport layer: This layer makes that the connection is reliable and authentic, allowing devices to continue talking to one another.
- Network access layer: This layer specifies the physical transport of the data. It covers the method through which hardware transmits data bits over actual cables or fibers.
- Application layer: This layer specifies how high-level apps can connect to the network and begin transferring data.
- Internet layer: This layer is in charge of encapsulating the data in decipherable packets and enabling transmission and reception.
The open systems interconnection (OSI) concept, which is comparable to TCP/IP but has seven layers instead of two, continues to have a significant influence on the structure of the modern internet.
Metropolitan area networks (MANs) and local area networks (LANs) are covered by the IEEE802 family of standards (MAN). The most well-known component of the IEEE 802 family is wireless LAN, also referred to as WLAN or Wi-Fis.
Networks can be categorized as follows according to organizational intent:
Internet: Several networks are joined by routers and stacked by networking software to form the internet (or the internetwork). Governments, researchers, businesses, the general public, and individual computer networks are all connected by this international system.
Extranet: Similar to an intranet, an extranet connects to specific external networks. It is typically used to share resources with business partners, clients, or distant workers.
Intranet: An intranet is a collection of networks maintained and managed by a single organization. Due to the limited access granted to authorized users, it is typically the most secure sort of network. In a local area network, the router is typically hidden by an intranet.
Darknet: The darknet is an internet-based overlay network that only specialist software may access. It makes use of particular, tailored communication protocols.
Key Objectives of Deploying Computer Network
Availability and dependability of resources
Performance supervision
Resource exchange
Higher storage capacit
Cost savings
Secured remote access
Streamlined collaboration & communication
Reduction of errors
Takeaway
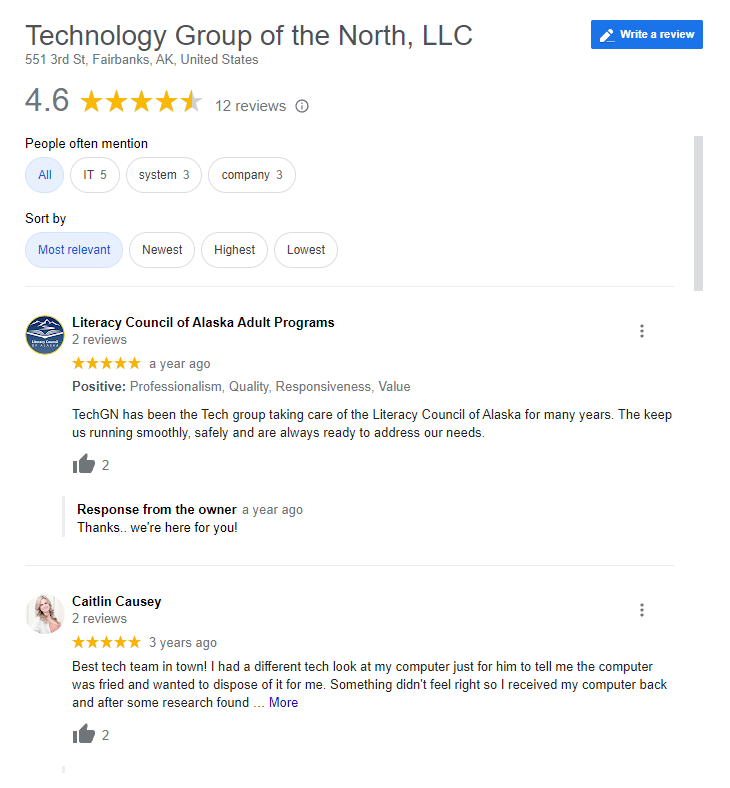
Reviews