Cybersecurity is the defense against cyberthreats for systems connected to the internet, including their hardware, software, and data. Individuals and businesses both utilize this technique to prevent illegal access to data centers and other digital systems.
A solid cybersecurity plan can offer a good security posture against malicious assaults intended to gain access to, alter, delete, destroy, or extort sensitive data and systems belonging to a business or user. Security measures are essential in preventing attacks that try to take down or impair a system or device’s functionality.
Cybercriminals are constantly looking for new ways to take advantage of holes in computer systems. And, regrettably, they are developing more sophisticated methods for conducting cyberattacks. The number of these cybercriminals is likewise increasing. The infrastructure of a person’s personal computer may also be destroyed by some. However, businesses and organizations are currently reevaluating their strategic planning against these kinds of attacks. Businesses and organizations are increasingly developing stronger strategies to stop further harm by employing cyber security managers or experts who recognize the need of keeping information secure and protected from these thieves.
Why is cybersecurity important?
The phrase can be broken down into a few basic categories and is used in a wide range of applications, including business and mobile computing.
Operational security covers the procedures and choices used to manage and safeguard data assets. This includes the policies that regulate how and where data may be stored or exchanged, as well as the permissions people have when accessing a network.
Network security The act of protecting a computer network from intruders, including malicious software that seizes opportunities or targeted attacks.
Information security Data integrity and privacy are safeguarded during storage and transmission
Application security aims to keep devices and software safe from harm. The data that an application is meant to safeguard may be accessible if it is compromised. Effective security starts at the design phase, long before a program or gadget is put into use.
End-user education deals with the aspect in cyber security that is most unpredictable: people. Anyone who disregards sound security procedures has the potential to unintentionally introduce a virus into a system that is otherwise secure. For the security of any firm, it is crucial to teach users to delete suspicious email attachments, to avoid plugging in unknown USB drives, and other key teachings.
Disaster recovery and business continuity How a company reacts to a cyber-security attack or any other situation that results in the loss of operations. Disaster recovery procedures specify how the organization restores its operations and information to resume normal business operations. The organization’s backup plan, when certain resources are unavailable, is business continuity.
For many firms, maintaining cybersecurity in a threat environment that is continuously changing is difficult. Traditional reactive strategies, which focused resources on defending systems against the most significant known threats while leaving less significant threats undefended, are no longer an effective method. An approach that is more proactive and adaptable is required to keep up with shifting security dangers. A number of significant cybersecurity consulting bodies provide direction. For instance, as part of a framework for risk assessment, the National Institute of Standards and Technology (NIST) advises adopting continuous monitoring and real-time assessments to protect against both known and unidentified threats.
What are the benefits of cybersecurity?
The advantages of putting cybersecurity procedures into place and sustaining them include:
- End-user and endpoint device security.
- Regulation observance.
- company continuity
- Increased trust from stakeholders, customers, partners, developers, and workers in the company’s reputation.
- Protection for businesses from cyberattacks and data breaches.
- Network and data protection.
- Preventing access by unauthorized users.
- Quicker recovery from a breach.
Different types of cybersecurity threats
Ransomware
Distributed denial-of-service (DDoS) attacks
Man-in-the-middle (MitM) attacks
Malware
Social engineering
Insider threats
Phishing
Advanced persistent threats (APTs)
SQL injection
A sort of cyber-attack called a SQL (structured language query) injection is used to take over and steal data from a database. Cybercriminals use malicious SQL statements to install malicious malware into databases by taking advantage of flaws in data-driven applications. They now have access to the delicate data stored in the database.
Botnets, drive-by-download attacks, exploit kits, malicious advertising, vishing, credential stuffing assaults, cross-site scripting (XSS) attacks, SQL injection attacks, business email compromise (BEC), and zero-day exploits are additional frequent forms of attacks.
What are the top cybersecurity challenges?
Hackers, data loss, privacy concerns, risk management, and evolving cybersecurity tactics all present ongoing threats to cybersecurity. In the foreseeable future, it is not anticipated that the number of cyberattacks would decline. Additionally, the emergence of the internet of things (IoT) and the resulting increase in attack entry points, as well as the expanding attack surface, make it more important than ever to protect networks and devices.
The data tsunami, the worker shortage and skills gap, the ever-evolving threats, the supply chain hazards, and cybersecurity awareness training are some of the major issues that need to be regularly addressed.
Cybersecurity awareness training
Education of end users should be included in cybersecurity efforts. On their computers or mobile devices, employees may unintentionally carry dangers and weaknesses into the office. They might also behave carelessly, such as downloading attachments or clicking links in phishing emails.
Employees who regularly receive security awareness training can help protect their firm from cyberthreats.
Supply chain attacks and third-party risks
Evolving threats
Workforce shortage and skills gap
Data deluge
Cyber safety tips
How can businesses and How can people and companies protect themselves against online threats? Here are our top advices for staying safe online:
- Antivirus software usage Threats will be found and eliminated by security tools like Kaspersky Total Security. For the best level of security, keep your software updated.
- Avoid using public WiFi networks that aren’t secure: You are more susceptible to man-in-the-middle attacks when using insecure networks. For the greatest performance, protection, and usability in a corporate endpoint security software in 2021, Kaspersky Endpoint Security won three AV-TEST awards. Kaspersky Endpoint Security demonstrated exceptional performance, protection, and usability for businesses in all tests.
- Update your software and operating system: You now have access to the most recent security updates.
- Clicking on links in emails from shady senders or unfamiliar websites is not advised: This is a typical method of how malware spreads.
- Utilize secure passwords: Make sure your passwords are difficult to guess.
- Never open email attachments from senders you don’t know: These might have malware on them.
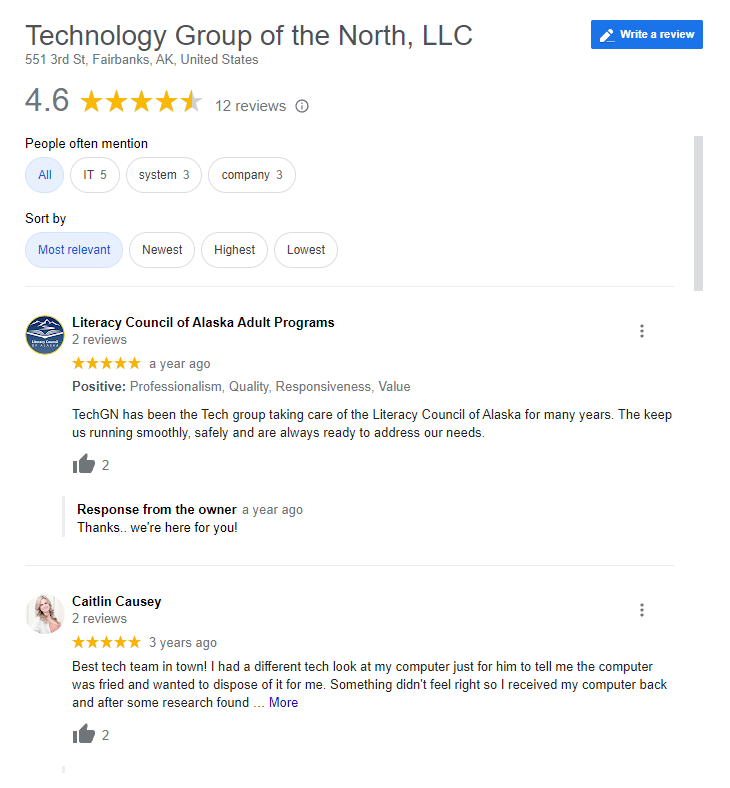
Reviews