In today’s fast-paced digital world, the security of financial transactions has never been more critical. With the rise of cyber threats and sophisticated hacking techniques, it’s essential to implement robust security measures to protect sensitive financial data. One of the most effective ways to enhance security in financial transactions is through secure hardware solutions. This blog post explores the importance of secure hardware in financial transactions, various types of secure hardware solutions, and best practices for implementation.
The Importance of Secure Hardware in Financial Transactions
Enhanced Security
Secure hardware provides a higher level of security compared to software-only solutions. By isolating critical security functions in dedicated hardware, the risk of unauthorized access or tampering is significantly reduced. This is particularly important in financial transactions where the stakes are high, and the consequences of a security breach can be devastating.
Trust and Integrity
Secure hardware solutions help establish trust and ensure the integrity of financial transactions. They provide a reliable environment where sensitive data can be processed securely, ensuring that transactions are genuine and have not been altered or intercepted.
Compliance with Regulations
Financial institutions are subject to stringent regulatory requirements to protect customer data and ensure transaction security. Implementing secure hardware solutions helps organizations comply with these regulations and avoid costly fines and penalties.
Types of Secure Hardware Solutions
Hardware Security Modules (HSMs)
HSMs are physical devices designed to manage and protect digital keys for strong authentication and encryption. They are used extensively in financial services to secure payment processing, safeguard sensitive data, and ensure the integrity of transactions. HSMs provide a tamper-resistant environment that can withstand physical and logical attacks.
Trusted Platform Modules (TPMs)
TPMs are specialized chips integrated into computer systems to enhance security. They store cryptographic keys and perform cryptographic operations, ensuring that sensitive data is protected at the hardware level. TPMs are commonly used in ATMs, point-of-sale (POS) systems, and other financial devices.
Secure Elements (SEs)
SEs are tamper-resistant microcontrollers used to store and manage sensitive information securely. They are widely used in mobile payment systems, smart cards, and contactless payment devices. SEs ensure that sensitive financial data, such as payment credentials, are protected from unauthorized access.
Best Practices for Implementing Secure Hardware Solutions
Conduct a Risk Assessment
Before implementing secure hardware solutions, it’s crucial to conduct a comprehensive risk assessment. Identify potential threats and vulnerabilities in your financial transaction processes and determine the appropriate hardware solutions to mitigate these risks.
Choose the Right Hardware
Select hardware solutions that meet your organization’s specific security requirements. Consider factors such as the level of security provided, ease of integration, and compliance with industry standards and regulations.
Implement Strong Access Controls
Ensure that access to secure hardware is strictly controlled and limited to authorized personnel only. Implement strong authentication mechanisms, such as multi-factor authentication (MFA), to prevent unauthorized access.
Regularly Update and Maintain Hardware
Keep secure hardware up to date with the latest firmware and security patches. Regularly inspect and maintain the hardware to ensure it remains in optimal condition and can effectively protect against emerging threats.
Train Staff on Security Protocols
Educate employees on the importance of secure hardware solutions and the role they play in protecting financial transactions. Provide training on security protocols and best practices to ensure that staff can effectively manage and operate secure hardware.
Monitor and Audit Transactions
Implement monitoring and auditing mechanisms to track and review financial transactions. This helps detect and respond to suspicious activities promptly, ensuring the continued security of financial transactions.
Bottom Line
As cyber threats continue to evolve, the need for secure hardware solutions in financial transactions becomes increasingly important. By implementing robust hardware security measures, financial institutions can protect sensitive data, maintain the integrity of transactions, and comply with regulatory requirements. Following best practices, such as conducting risk assessments, choosing the right hardware, and implementing strong access controls, can help organizations enhance the security of their financial transactions and build trust with their customers.
Secure hardware solutions are a critical component in the fight against cyber threats in the financial sector. By investing in and properly managing these solutions, organizations can ensure that their financial transactions remain secure in an ever-changing digital landscape.
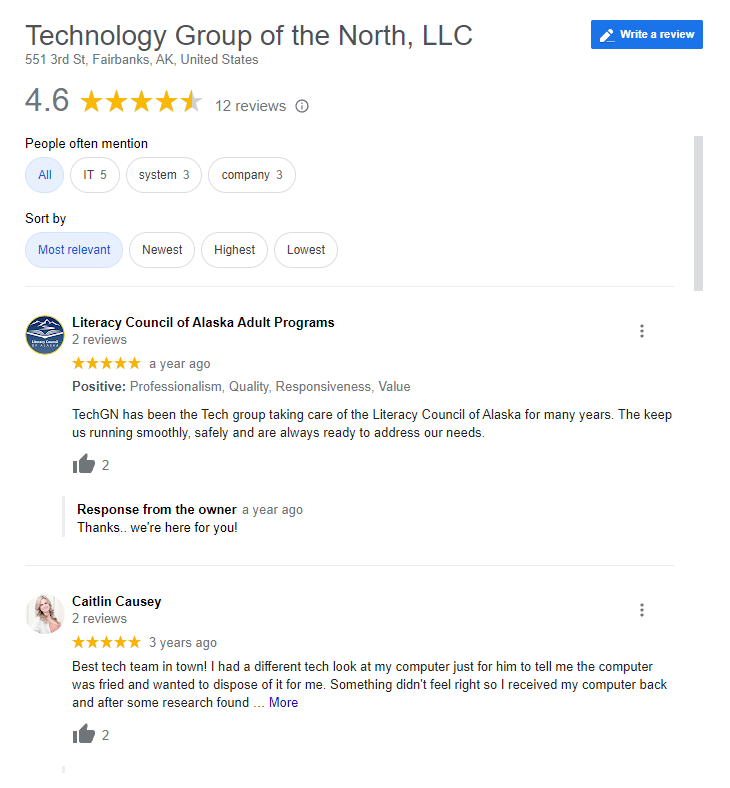
Reviews
Tailoring Solutions