Holy Week is a time of reflection, travel, and reduced business activity. Across countries like the Philippines, where observances such as Holy Thursday and Good Friday are widely practiced, many businesses operate with minimal staff or close temporarily.
Unfortunately, cybercriminals are well aware of this pattern.
Holiday periods, including Holy Week, create the perfect opportunity for attackers to launch phishing campaigns. With fewer employees monitoring systems and an increase in online transactions, businesses become more vulnerable to holiday phishing scams.
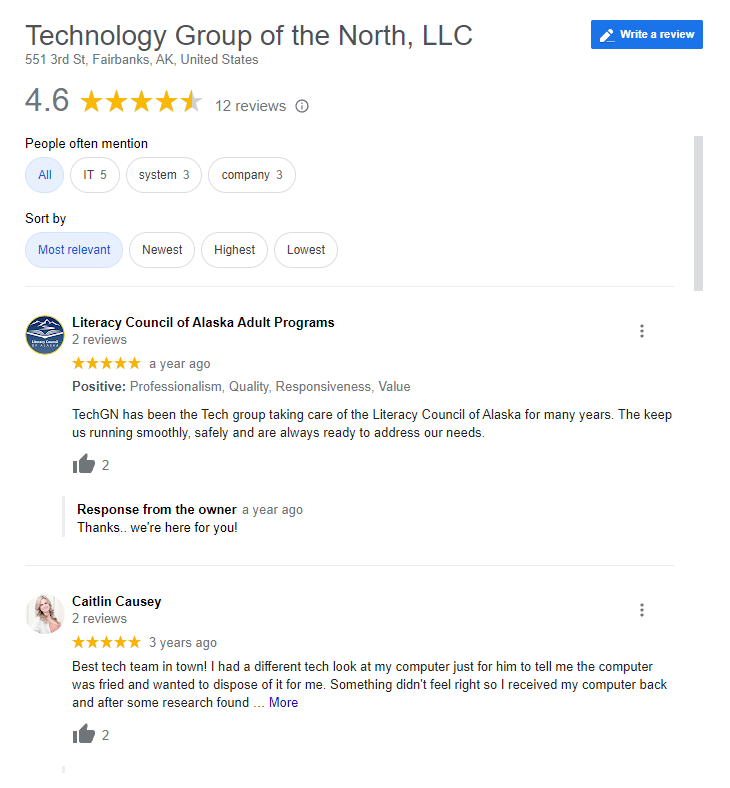
At TechGN, we’ve observed a significant spike in cyberattacks during holiday seasons. This comprehensive guide will help you understand these threats, recognize warning signs, and implement strong defenses to protect your organization.
What Are Holiday Phishing Scams?
Holiday phishing scams are deceptive cyberattacks designed to trick individuals into revealing sensitive information such as login credentials, financial data, or company access details.
These scams are often disguised as:
- Shipping updates
- Payment confirmations
- Holiday promotions
- Travel itineraries
- Internal company messages
During Holy Week, attackers tailor their messages to match seasonal behavior. For example, they may impersonate religious organizations, travel agencies, or even internal staff requesting urgent approvals before the holiday break.
Why Holy Week Is a Prime Target for Cybercriminals
Cybercriminals rely on timing and human behavior. Holy Week presents several advantages for attackers.
First, many employees are out of the office or working reduced hours. This means fewer people are available to verify suspicious emails or requests.
Second, businesses often rush to complete transactions before closing. This urgency makes employees more likely to act quickly without verifying authenticity.
Third, increased online activity, such as travel bookings, online shopping, and donations creates more opportunities for phishing attempts.
Finally, IT teams may also be operating with limited capacity, delaying response times to potential threats.
These factors combined make Holy Week one of the most overlooked yet dangerous periods for cybersecurity.
Common Types of Holiday Phishing Scams
1. Fake Shipping Notifications
Attackers send emails that appear to come from logistics companies, claiming a delivery issue or requiring confirmation. These emails often contain malicious links.
2. Travel and Booking Scams
With many people traveling during Holy Week, cybercriminals impersonate airlines or hotels. Victims are asked to confirm bookings or update payment details.
3. Donation and Charity Scams
Religious observances often involve charitable giving. Attackers exploit this by creating fake donation campaigns that redirect funds.
4. Urgent Business Requests
Employees may receive emails that appear to come from executives requesting urgent payments or sensitive information before the holiday closure.
5. Account Security Alerts
Fake alerts claiming suspicious activity prompt users to “secure” their accounts by entering credentials on fraudulent websites.
How Phishing Attacks Work
Phishing attacks typically follow a structured process.
The attacker first researches their target, often gathering information from social media or company websites. This helps them craft convincing messages.
Next, they create an email or message that appears legitimate. It may include official logos, familiar language, and urgent instructions.
Once the victim interacts with the message by clicking a link or downloading an attachment, they are redirected to a fake website or unknowingly install malware.
Finally, the attacker collects the stolen information or gains access to systems, which can lead to further attacks such as ransomware or data breaches.
Warning Signs of Holiday Phishing Scams
Recognizing phishing attempts is the first line of defense. While attackers are becoming more sophisticated, there are still common red flags.
Emails that create a sense of urgency should always be treated with caution. Messages that demand immediate action, especially involving financial transactions, are often malicious.
Another warning sign is mismatched email addresses. Even if the display name looks familiar, the actual email domain may reveal inconsistencies.
Poor grammar or unusual phrasing can also indicate a phishing attempt, although many modern scams are now well-written.
Suspicious links are another major indicator. Hovering over a link often reveals a URL that does not match the supposed sender.
Unexpected attachments should never be opened without verification, especially during holiday periods when attackers expect reduced scrutiny.
The Business Impact of Falling for Phishing Scams
The consequences of phishing attacks can be severe.
Financial loss is one of the most immediate impacts. Businesses may unknowingly transfer funds to fraudulent accounts or face unauthorized transactions.
Data breaches are another major concern. Sensitive customer information, employee data, and proprietary business information can be exposed.
Operational disruption often follows. Systems may need to be shut down, investigated, and restored, leading to downtime and lost productivity.
Reputational damage can also be long-lasting. Customers and partners may lose trust in a business that fails to protect its data.
In some cases, companies may face legal and compliance penalties, especially if they operate in regulated industries.
How to Protect Your Business During Holy Week
Effective cybersecurity requires a proactive approach, especially during high-risk periods like Holy Week.
Start by strengthening email security systems. Advanced filtering tools can detect and block phishing attempts before they reach employees. Multi-factor authentication adds an extra layer of protection, ensuring that stolen credentials alone are not enough to gain access.
Employee awareness is critical. Regular training helps staff recognize phishing attempts and respond appropriately.
Businesses should also implement clear verification processes for financial transactions. Any request involving payments or sensitive information should be confirmed through a secondary channel.
Regular system updates and patches ensure that vulnerabilities are minimized. Finally, having an incident response plan in place allows businesses to act quickly if a phishing attack occurs.
The Role of Cybersecurity Solutions
Modern cybersecurity solutions play a crucial role in preventing phishing attacks. Email security platforms use artificial intelligence to detect suspicious patterns and block malicious messages.
Endpoint protection systems monitor devices for unusual activity and prevent malware from spreading. Identity and access management tools ensure that only authorized users can access critical systems.
Security monitoring and analytics provide real-time insights into potential threats, allowing businesses to respond quickly. At TechGN, we integrate these solutions into a unified cybersecurity strategy tailored to each client’s needs.
Real-World Scenario: A Holiday Phishing Attack
Imagine a company preparing to close for Holy Week. An employee receives an email from what appears to be the finance department requesting an urgent payment to a supplier.
The email looks legitimate and includes accurate company details. With the pressure to complete tasks before the holiday, the employee processes the payment without verification.
Days later, the company discovers that the email was fraudulent and the funds are gone.
This scenario is more common than many realize. It highlights the importance of vigilance, even during busy or relaxed periods.
Why Employee Awareness Is Your Strongest Defense
Technology alone cannot prevent all phishing attacks. Human awareness remains a critical factor.
Employees should be trained to question unexpected requests, especially those involving urgency or sensitive information.
Encouraging a culture of caution can significantly reduce the risk of successful attacks. Staff should feel comfortable reporting suspicious messages without fear of consequences.
Regular simulations and training exercises help reinforce these behaviors and keep cybersecurity top of mind.
Future Trends in Phishing Attacks
Phishing attacks are becoming more advanced with the use of artificial intelligence and automation.
Attackers can now create highly personalized messages that are difficult to distinguish from legitimate communication.
Deepfake technology and voice phishing (vishing) are also emerging threats, allowing attackers to impersonate individuals more convincingly.
As these threats evolve, businesses must adopt more sophisticated defenses and stay informed about the latest cybersecurity trends.
Don’t let cybercriminals take advantage of your business during the holidays.
Protect your organization with expert cybersecurity solutions from TechGN. Our team is ready to help you identify risks, strengthen defenses, and ensure your systems remain secure year-round.
👉 Visit https://techgn.com/ today to schedule your cybersecurity consultation and safeguard your business against evolving threats.
Reviews
Tailoring Solutions