Cyber threats continue to grow every year, putting businesses of all sizes at risk. From phishing attacks and ransomware to credential theft and identity fraud, cybercriminals constantly search for weaknesses in digital systems. One of the most effective ways to defend against these threats is multi-factor authentication in cybersecurity.
Passwords alone are no longer enough to secure sensitive systems, cloud platforms, and business networks. Cybercriminals have become extremely skilled at stealing credentials through data breaches, malware, or social engineering. Even strong passwords can be compromised.
This is why security experts and IT providers increasingly recommend multi-factor authentication (MFA) as a standard protection layer. By requiring more than one form of verification before granting access, MFA dramatically reduces the risk of unauthorized entry.
At TechGN, we help organizations strengthen their cybersecurity posture through advanced security strategies, including multi-factor authentication implementation, endpoint protection, identity management, and network security solutions. Businesses that adopt MFA significantly reduce their exposure to cyber threats and data breaches.
Understanding how multi-factor authentication in cybersecurity works and why it matters is essential for modern businesses that rely on digital systems and cloud technology.
Understanding Multi-Factor Authentication in Cybersecurity
Multi-factor authentication is a security mechanism that requires users to verify their identity using two or more authentication factors before gaining access to a system, application, or network.
Traditional login systems rely only on a username and password, which is considered a single-factor authentication method. Unfortunately, passwords are vulnerable to hacking techniques such as:
- Phishing attacks
- Credential stuffing
- Brute-force attacks
- Keylogging malware
- Data breaches
Multi-factor authentication adds additional layers of verification, making it significantly harder for attackers to gain access even if they have stolen a password.
The concept behind multi-factor authentication in cybersecurity is based on three main identity categories:
Something You Know
This refers to information the user knows.
Examples include:
- Passwords
- PIN codes
- Security questions
While passwords remain a common authentication method, they are also the weakest layer when used alone.
Something You Have
This refers to a physical device or token possessed by the user.
Examples include:
- Mobile authentication apps
- Security tokens
- Smart cards
- SMS verification codes
Even if an attacker steals a password, they still cannot access the account without the physical device.
Something You Are
This refers to biometric identification.
Examples include:
- Fingerprint recognition
- Facial recognition
- Retina scans
- Voice recognition
Biometric authentication is becoming increasingly common in smartphones, enterprise security systems, and financial applications.
By combining two or more of these authentication factors, multi-factor authentication in cybersecurity creates a strong defense against unauthorized access.
Why Passwords Alone Are No Longer Secure
Many organizations still rely solely on passwords for authentication. Unfortunately, this approach is no longer effective against modern cyber threats.
Cybercriminals have developed advanced techniques to compromise passwords quickly and efficiently.
Password Reuse
One of the most common security problems is password reuse. Many users use the same password across multiple platforms, including:
- Email accounts
- Corporate systems
- Social media
- Cloud storage platforms
If a single service experiences a data breach, attackers can use those credentials to access other accounts.
Phishing Attacks
Phishing is one of the most successful hacking techniques. Attackers send fake emails that appear to come from trusted sources, tricking users into revealing their passwords.
Once the password is stolen, attackers can easily access accounts if no additional authentication is required.
Credential Stuffing
Credential stuffing attacks occur when hackers use large databases of leaked passwords from previous data breaches. Automated tools attempt to log into thousands of systems using these stolen credentials.
Without multi-factor authentication in cybersecurity, these attacks can succeed quickly.
Brute Force Attacks
Brute force attacks involve automated tools that guess passwords repeatedly until the correct one is found. Weak passwords are especially vulnerable to this method.
Because passwords alone are vulnerable, cybersecurity professionals recommend multi-factor authentication as a standard security measure.
How Multi-Factor Authentication Prevents Cyber Attacks
Implementing multi-factor authentication in cybersecurity significantly reduces the chances of unauthorized access.
Even if an attacker manages to steal login credentials, they still cannot bypass the additional authentication layers.
Here are several ways MFA protects businesses from cyber threats.
Protection Against Credential Theft
Stolen credentials are responsible for a large percentage of data breaches. MFA prevents attackers from accessing systems even if passwords are compromised.
For example:
A hacker may obtain an employee’s password through phishing. However, when attempting to log in, the system requests a verification code from the employee’s mobile device. Without access to that device, the attacker cannot proceed.
Defense Against Phishing Attacks
Phishing attacks are less effective when MFA is enabled. Even if a user accidentally reveals their password, the attacker cannot complete the login process without the second authentication factor.
Reduced Risk of Account Takeover
Account takeover attacks occur when hackers gain control of user accounts. MFA prevents these attacks by requiring additional verification.
This is especially important for:
- Email accounts
- Financial systems
- Remote work platforms
- Cloud storage services
Secure Remote Work Environments
With remote work becoming more common, employees often access company systems from various locations and devices.
Multi-factor authentication ensures that only verified users can access sensitive systems, regardless of location.
At TechGN, we often recommend MFA for companies that rely on remote IT infrastructure, cloud applications, and virtual private networks (VPNs).
Types of Multi-Factor Authentication Methods
Organizations can implement several types of authentication methods depending on their security requirements.
Authentication Apps
Authentication apps generate time-based verification codes used during login.
Common examples include:
- Microsoft Authenticator
- Google Authenticator
- Duo Mobile
These apps are widely used because they provide strong security without relying on SMS messages.
SMS Verification Codes
SMS authentication sends a one-time password (OTP) to the user’s mobile phone.
While SMS MFA is better than passwords alone, it is considered less secure than authentication apps due to risks such as SIM swapping.
Hardware Security Tokens
Hardware tokens generate authentication codes or connect via USB or NFC.
Examples include:
- YubiKey
- Smart card authentication
Hardware tokens are commonly used by government agencies and high-security organizations.
Biometric Authentication
Biometric verification uses unique physical characteristics to verify identity.
Examples include:
- Facial recognition
- Fingerprint scanning
- Retina recognition
Biometric authentication is increasingly used in mobile devices and enterprise security platforms.
Push Notification Authentication
Push-based authentication sends a notification to a user’s smartphone asking them to approve or deny a login attempt.
This method improves both security and user convenience.
Industries That Benefit Most From Multi-Factor Authentication
Although multi-factor authentication in cybersecurity is valuable for every organization, certain industries face especially high risks.
Financial Services
Banks and financial institutions handle extremely sensitive financial data. MFA is essential for protecting online banking systems and preventing fraud.
Healthcare
Healthcare organizations store large amounts of personal medical data. Regulations such as HIPAA compliance require strong security protections.
MFA helps protect patient records and healthcare management systems.
Government Agencies
Government networks often contain classified or sensitive data. Multi-factor authentication is commonly required for secure access.
Technology Companies
Technology companies rely heavily on cloud platforms, development systems, and remote collaboration tools. MFA protects intellectual property and corporate data.
Small and Medium Businesses
Small businesses are increasingly targeted by cybercriminals because they often lack strong security systems.
Implementing MFA is one of the easiest ways to strengthen security without large infrastructure investments.
At TechGN, we frequently help small and mid-sized organizations implement multi-factor authentication solutions that integrate with cloud services, Microsoft 365, and remote work systems.
Multi-Factor Authentication and Cloud Security
Cloud computing platforms such as Microsoft 365, Google Workspace, and Amazon Web Services (AWS) have become essential tools for modern businesses.
However, cloud accounts are prime targets for cybercriminals.
Once attackers gain access to cloud accounts, they can:
- Download sensitive business data
- Send phishing emails from legitimate accounts
- Install malicious software
- Disrupt operations
Implementing multi-factor authentication in cybersecurity ensures that cloud environments remain protected even if passwords are compromised.
Cloud providers now strongly recommend or require MFA for administrative accounts.
Organizations that fail to enable MFA leave themselves vulnerable to major security risks.
Compliance and Regulatory Requirements
Many cybersecurity regulations now require or strongly recommend multi-factor authentication.
These regulations include:
- HIPAA (Healthcare data protection)
- PCI DSS (Payment card security)
- GDPR (European data protection regulations)
- SOC 2 compliance standards
Organizations that fail to implement strong authentication systems may face:
- Regulatory penalties
- Financial losses
- Legal liability
- Reputational damage
Adopting multi-factor authentication in cybersecurity helps businesses maintain compliance while protecting their systems and customers.
Challenges Businesses Face When Implementing MFA
While MFA significantly improves security, some businesses hesitate to adopt it due to concerns about complexity or user inconvenience.
Common concerns include:
User Resistance
Employees sometimes view MFA as an extra step that slows down login processes. Proper training and user-friendly authentication methods can reduce this issue.
Integration With Existing Systems
Older software systems may not support modern authentication protocols. In these cases, IT professionals may need to implement additional identity management solutions.
Device Management
Organizations must ensure that authentication devices such as smartphones or tokens are securely managed.
Despite these challenges, the benefits of MFA far outweigh the drawbacks.
Best Practices for Implementing Multi-Factor Authentication
To maximize the effectiveness of multi-factor authentication in cybersecurity, businesses should follow several best practices.
Apply MFA to All Critical Systems
Organizations should prioritize MFA for systems that contain sensitive information.
Examples include:
- Email systems
- Cloud platforms
- Financial software
- Remote access systems
Use Strong Authentication Methods
Authentication apps or hardware tokens are generally more secure than SMS codes.
Train Employees on Cybersecurity Awareness
Users must understand why MFA is important and how to recognize phishing attempts.
Implement Identity and Access Management
Combining MFA with identity and access management (IAM) helps control who can access specific systems and data.
Monitor Login Activity
Organizations should monitor login attempts to detect suspicious activity or unauthorized access attempts.
At TechGN, we work closely with businesses to design secure authentication frameworks that align with industry standards and operational needs.
The Future of Authentication and Cybersecurity
Cybersecurity continues to evolve as attackers develop new methods to bypass traditional security systems.
Future authentication technologies may include:
- Passwordless authentication systems
- Behavioral biometrics
- AI-powered identity verification
- Zero Trust security frameworks
Passwordless security solutions are gaining popularity because they eliminate password-related vulnerabilities entirely.
Many organizations are now combining multi-factor authentication with Zero Trust security models, which assume that every user and device must be verified continuously.
This approach provides a much stronger defense against modern cyber threats.
Strengthen Your Cybersecurity With TechGN
Cybersecurity threats are increasing every year, and businesses must take proactive steps to protect their systems, data, and employees.
Implementing multi-factor authentication in cybersecurity is one of the most effective and affordable ways to reduce the risk of cyber attacks.
At TechGN, we provide advanced cybersecurity solutions designed to protect organizations from evolving digital threats. Our services include:
- Cybersecurity risk assessments
- Multi-factor authentication deployment
- Network security and firewall management
- Endpoint protection and threat detection
- Cloud security solutions
- Business IT support and infrastructure management
Whether your organization needs help implementing MFA, securing cloud platforms, or building a comprehensive cybersecurity strategy, our team can provide the expertise you need.
Protect your business before cyber threats strike.
Contact TechGN today to strengthen your cybersecurity and implement multi-factor authentication across your organization. Learn more about our cybersecurity services and IT solutions designed to keep your business safe in an increasingly digital world.
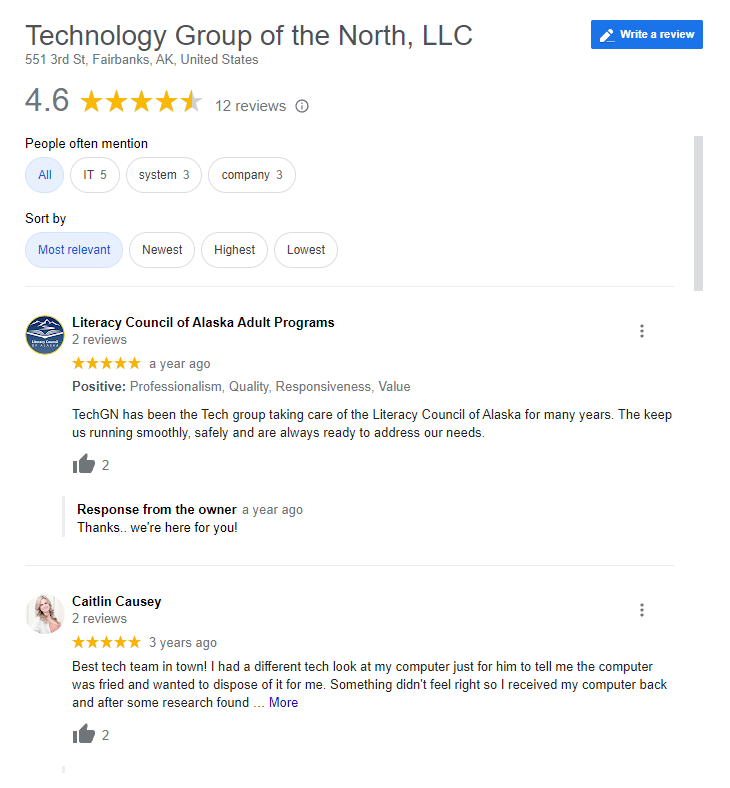
Reviews
Tailoring Solutions